Mastering Winbox login Your comprehensive guide to accessing MikroTik routers securely and efficiently
If you’re managing a MikroTik router, one of the first steps you’ll take is to log into the device using Winbox. The Winbox login process is vital for configuring, monitoring, and securing your network. Whether you’re a network administrator or an enthusiast, understanding how to navigate Winbox login efficiently can save you time and ensure your network remains protected. This guide explores every critical aspect of seamlessly accessing your MikroTik device via Winbox, ensuring you are well-equipped to handle your router’s administration with confidence.
The importance of understanding Winbox login in network management
Efficient network management hinges on reliable access to your devices. Winbox, as MikroTik’s graphical management tool, provides a straightforward way to connect to routers, set configurations, and troubleshoot issues. The process of Winbox login is more than just entering credentials; it involves understanding connection protocols, security best practices, and troubleshooting potential issues that may prevent successful login.
Comprehending the significance of Winbox login extends beyond basic access; it ensures the confidentiality and integrity of network configurations. In today’s rapidly evolving cyber environment, securing access credentials and understanding login procedures prevent unauthorized access and potential network breaches. This section emphasizes why mastering the Winbox login process is fundamental for maintaining a resilient and secure network infrastructure.
Furthermore, a smooth Winbox login experience improves operational efficiency. Repeated login failures or misconfigurations can delay essential network maintenance, affecting overall performance. As such, having a deep understanding of login procedures, troubleshooting common issues, and embracing security measures can make network management more reliable and less prone to errors.
Preparing for Winbox login: prerequisites and initial setup

Before attempting to login via Winbox, several preparations are necessary to ensure a seamless connection. Proper setup avoids common pitfalls like incorrect credentials, network restrictions, or device misconfigurations that hinder access. This section guides you through the essential steps to prepare your environment for efficient Winbox login.
Checking network connectivity and device readiness
A fundamental prerequisite for Winbox login is verifying that your computer and the MikroTik router are on the same network or can communicate over the network. Ensuring that both devices are connected via Ethernet or Wi-Fi with valid IP addresses reduces the risk of connectivity issues.
Use command prompt or terminal commands like ping to check connectivity:
ping 192.168.88.1Replace 192.168.88.1 with the router’s IP address. If the ping is successful, the network connection is active; if not, troubleshoot network settings or physical connections.
Ensure that the router is powered on and responsive. Sometimes, physical issues or power outages can prevent access. Confirming the device’s operational status helps eliminate basic issues before attempting to log in.
Configuring IP addresses and default settings
The default IP address for MikroTik routers is often 192.168.88.1. If the IP address has been changed or is unknown, connect via a direct serial connection or reset the device to factory settings for a fresh start. This guarantees that the device’s management IP address is accessible.
In addition, manage default passwords, which are usually set to ‘admin’ with no password or ‘admin’ without a password. For security, change default credentials immediately after first login to prevent unauthorized access.
Installing and setting up Winbox
While Winbox is a standalone application that can be downloaded from the MikroTik website, ensuring you have the latest version facilitates compatibility and security. Download the application to your computer, and consider running it with administrator privileges to avoid common permission issues.
Once installed, add Winbox to your trusted applications list, especially if you use firewalls or antivirus software. Proper setup enhances stability and prevents connection disruptions during login sessions.
Security considerations before login
Securing your login process is essential. Always connect over secure networks, avoid public Wi-Fi when managing critical routers, and employ VPNs if necessary for remote access. Configuring strong, unique passwords for your MikroTik device minimizes the risk of unauthorized access.
Additionally, enable firewall rules that restrict Winbox access to trusted IP addresses. This proactive security measure ensures that only authorized personnel can attempt Winbox login, reducing vulnerability exposure.
How to access your MikroTik router via Winbox – step-by-step guide
Successfully logging into your MikroTik router through Winbox is straightforward when following the correct procedure. Whether connecting locally or remotely, understanding each step enhances your efficiency and security. This section provides an in-depth walkthrough for a smooth Winbox login process, including verification steps, common pitfalls, and advanced tips for experienced users.
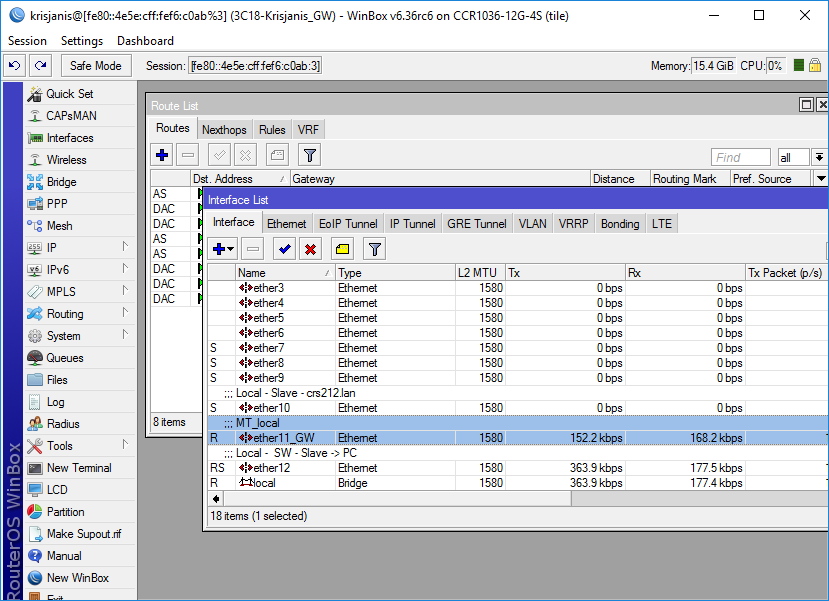
Launching Winbox and selecting the device
Start by opening the Winbox application on your computer. Upon launch, Winbox scans the local network and displays a list of available MikroTik devices. This device discovery feature simplifies rapid access to routers, especially in environments with multiple MikroTik units.
If your device does not appear in the list, you can manually enter the router’s IP address or MAC address into the Winbox connect window. Using MAC addresses is particularly useful if IP addresses are dynamic or unknown.
Entering credentials and connecting securely
In the Winbox login window, choose the correct interface—whether connecting via MAC address or IP. Enter your username and password, ensuring they are accurate and securely stored. For first-time access, default credentials are often admin with no password, but it is highly recommended to change them immediately after login.
To enhance connection security:
- Use the ‘Secure Password’ feature to encrypt credentials
- Check ‘Connect Automatically’ for convenience in recurring access
- Enable TLS or SSH tunneling if remotely accessing the router
After entering credentials, click on ‘Connect.’ Winbox then authenticates with the router, and upon success, opens the management interface.
Troubleshooting common login issues
Sometimes, login attempts fail due to various issues such as wrong credentials, network problems, or device misconfigurations. Troubleshooting effectively involves:
- Verifying the correct IP address or MAC address
- Confirming that the username/password combo is correct
- Ensuring that firewall rules do not block Winbox traffic
- Checking that the router is reachable over the network
If login fails, reviewing log files or running diagnostic commands through alternative access methods like telnet or SSH can reveal underlying issues. Resetting the device to factory settings is a last resort if credentials or configurations are unknown or corrupted.
Advanced tips for premium Winbox connection
For advanced users, securing Winbox connections through VPN tunnels or encrypted links (like SSH) adds an extra layer of security. Pinpointing specific port numbers for connection (default is 8291) can streamline access in complex network environments. Bookmark your device’s MAC address or IP for faster recovery after reboots or network changes.
To automate access, consider scripting login procedures with scripts or APIs. This allows for rapid configuration changes and monitoring, especially in large-scale deployments.
Troubleshooting and security best practices for Winbox login
Ensuring reliable access and maintaining secure environment practices are crucial for any network administrator. This section discusses common issues that may occur during Winbox login and shares best practices to prevent security breaches or disruptions.
Troubleshooting common Winbox login problems
Network issues are the leading cause of Winbox login failures. If typical troubleshooting steps like ping tests, verifying IP addresses, and reconnecting do not resolve the problem, consider deeper diagnostics:
- Check the Winbox logs for error messages
- Confirm no IP or MAC filtering rules prevent access
- Temporarily disable firewalls that may block the connection
- Use alternative connection methods like SSH or serial console for legacy devices
Sometimes, the problem lies within the router’s configuration itself—incorrect user permissions or disabled Winbox service can prevent login. Understanding router logs and configuration states helps in pinpointing issues swiftly.
Security vulnerabilities associated with Winbox login
Despite Winbox’s widespread popularity, certain vulnerabilities can be exploited in poorly secured networks. For example:
- Default credentials that are not changed pose a major risk
- Lack of encrypted connections (using plaintext protocols)
- Open ports accessible from unmanaged networks
These weaknesses expose routers to unauthorized access, configuration changes, or worse, malicious attacks. Regular vulnerability assessments and firmware updates are essential.
Best practices to safeguard your login credentials
Protecting login credentials is paramount. Use complex, unique passwords and change them periodically. Implement multi-factor authentication if supported, especially for remote access scenarios.
Limit Winbox access to known IP addresses through firewall rules. Always use secure channels like VPNs or SSH tunneling for remote login. Disable Winbox service altogether on devices where remote access isn’t needed, or restrict access to specific times.
Furthermore, keep your MikroTik firmware updated with the latest security patches, and enable logging for login attempts to monitor suspicious activity. These proactive measures significantly diminish the likelihood of compromise.
Comparative analysis of different MikroTik access methods – what to choose?
While Winbox remains the most popular management tool for MikroTik, alternative access methods exist, each with its advantages and limitations. This section compares Winbox with other approaches to help you select the appropriate method for your needs.
| Method | Security Level | Ease of Use | Remote Access | Suitable Scenarios |
|---|---|---|---|---|
| Winbox (GUI) | Moderate to High | High | Yes (with VPN) | Local and remote management |
| WebFig (Browser-based UI) | Moderate | Moderate | Yes | Quick configuration, minimal setup |
| SSH terminal | High | Moderate | Yes | Advanced troubleshooting, scripting |
| Telnet | Low | High | Yes | Legacy systems, low security |
| Command-line scripts | High | Moderate | Yes | Automated management |
Understanding these options enables administrators to adapt to various operational environments, balancing convenience and security. Winbox’s graphical interface is highly favored for day-to-day management due to its user-friendliness and feature richness, but for remote access, SSH with tunneling or VPNs enhances security.
Choosing the right method depends on your specific security policies, technical expertise, and operational requirements. Combining multiple approaches often yields the most flexible and secure network management strategy.
Conclusion
The Winbox login process is the gateway to effective MikroTik router management, combining user-friendly access with powerful configuration capabilities. Ensuring a smooth login involves thorough preparation, understanding network environments, and prioritizing security practices. Whether managing devices locally or remotely, mastering Winbox login boosts operational efficiency, enhances network security, and minimizes downtime. As network complexities grow, so does the importance of secure, reliable access methods. Continually updating your knowledge and best practices ensures your MikroTik management remains robust, responsive, and resilient against evolving threats.

